Reset WP Password using Plesk’s WordPress Toolkit (For Plesk Onyx 17.8 and newer):
1. Log into Plesk
2. Navigate to Domains > example.com > WordPress_instance_name > setup:
3. Specify a new password and press ChangeReset the WordPress Admin password via Email by clicking on Lost Your Password link:
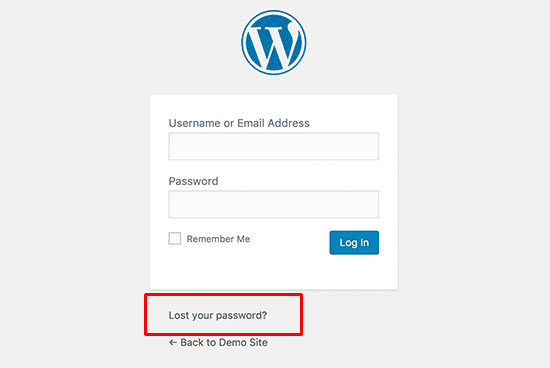
Please Note: The password recovery email will be sent to your mailbox on file when you setup this WordPress site.
Reset WordPress Password in MySQL Database from phpMyAdmin:
1. Begin by logging into phpMyAdmin and clicking Databases
2. A list of databases will appear, click on the proper WordPress database: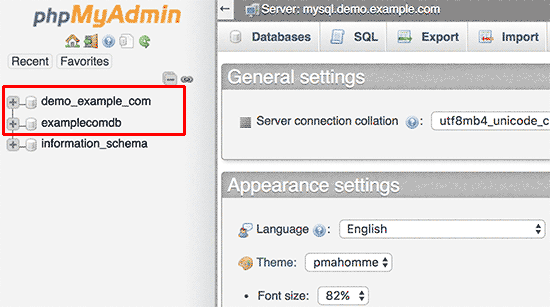
3. You will see the list of tables in your WordPress database. Now you need to look for table “table-prefix_users” such as “wp_users”.
4. Click on the icon for Browse: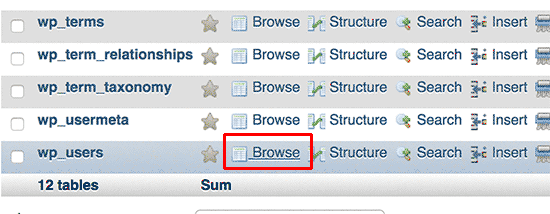
5. Locate your username under “user_login” and click on Edit (may look like a pencil icon in some versions of phpMyAdmin)
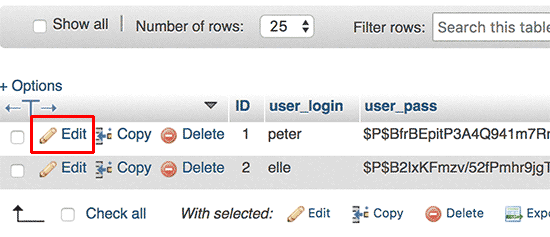
6. Select MD5 from the drop down menu under “user_pass”, then delete the Value and replace it with your new password.
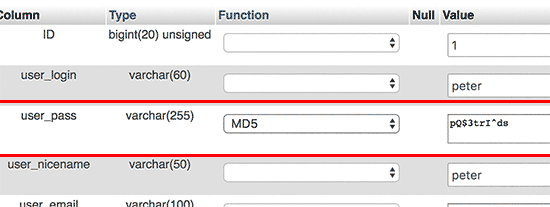
7. Click on “Go” button to save the changes. Your password will be encrypted using the MD5 hash and then it will be stored in the database
8. Congratulations ! You have successfully changed your WordPress password using phpMyAdmin.Using the Emergency Password Reset Script:
If the other solutions listed above won’t work, then try the Emergency Password Reset Script. It is not a Plugin. It is a PHP script.
- Warnings
- Requires you know the administrator username.
- It updates the administrator password and sends an email to the administrator’s email address.
- If you don’t receive the email, the password is still changed.
- You do not need to be logged in to use it. If you could login, you wouldn’t need the script.
- Place this in the root of your WordPress installation. Do not upload this to your WordPress Plugins directory.
- Delete the script when you are done for security reasons.
- Directions for use
- Save the script below as a file called emergency.php to the root of your WordPress installation (the same directory that contains wp-config.php).
- In your browser, open http://example.com/emergency.php
- As instructed, enter the administrator username (usually admin) and the new password, then click Update Options. A message is displayed noting the changed password. An email is sent to the blog administrator with the changed password information.
- Delete emergency.php from your server when you are done. Do not leave it on your server as someone else could use it to change your password.
<?php /* This program is free software; you can redistribute it and/or modify it under the terms of the GNU General Public License as published by the Free Software Foundation; either version 2 of the License, or (at your option) any later version. This program is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the GNU General Public License for more details. You should have received a copy of the GNU General Public License along with this program; if not, write to the Free Software Foundation, Inc., 59 Temple Place, Suite 330, Boston, MA 02111-1307 USA */ require './wp-blog-header.php'; function meh() { global $wpdb; if ( isset( $_POST['update'] ) ) { $user_login = ( empty( $_POST['e-name'] ) ? '' : sanitize_user( $_POST['e-name'] ) ); $user_pass = ( empty( $_POST[ 'e-pass' ] ) ? '' : $_POST['e-pass'] ); $answer = ( empty( $user_login ) ? '<div id="message" class="updated fade"><p><strong>The user name field is empty.</strong></p></div>' : '' ); $answer .= ( empty( $user_pass ) ? '<div id="message" class="updated fade"><p><strong>The password field is empty.</strong></p></div>' : '' ); if ( $user_login != $wpdb->get_var( "SELECT user_login FROM $wpdb->users WHERE ID = '1' LIMIT 1" ) ) { $answer .="<div id='message' class='updated fade'><p><strong>That is not the correct administrator username.</strong></p></div>"; } if ( empty( $answer ) ) { $wpdb->query( "UPDATE $wpdb->users SET user_pass = MD5('$user_pass'), user_activation_key = '' WHERE user_login = '$user_login'" ); $plaintext_pass = $user_pass; $message = __( 'Someone, hopefully you, has reset the Administrator password for your WordPress blog. Details follow:' ). "\r\n"; $message .= sprintf( __( 'Username: %s' ), $user_login ) . "\r\n"; $message .= sprintf( __( 'Password: %s' ), $plaintext_pass ) . "\r\n"; @wp_mail( get_option( 'admin_email' ), sprintf( __( '[%s] Your WordPress administrator password has been changed!' ), get_option( 'blogname' ) ), $message ); $answer="<div id='message' class='updated fade'><p><strong>Your password has been successfully changed</strong></p><p><strong>An e-mail with this information has been dispatched to the WordPress blog administrator</strong></p><p><strong>You should now delete this file off your server. DO NOT LEAVE IT UP FOR SOMEONE ELSE TO FIND!</strong></p></div>"; } } return empty( $answer ) ? false : $answer; } $answer = meh(); ?> <!DOCTYPE html PUBLIC "-//W3C//DTD XHTML 1.0 Transitional//EN" "http://www.w3.org/TR/xhtml1/DTD/xhtml1-transitional.dtd"> <html xmlns="http://www.w3.org/1999/xhtml"> <head> <title>WordPress Emergency PassWord Reset</title> <meta http-equiv="Content-Type" content="<?php bloginfo( 'html_type' ); ?>; charset=<?php bloginfo( 'charset' ); ?>" /> <link rel="stylesheet" href="<?php bloginfo( 'wpurl' ); ?>/wp-admin/wp-admin.css?version=<?php bloginfo( 'version' ); ?>" type="text/css" /> </head> <body> <div class="wrap"> <form method="post" action=""> <h2>WordPress Emergency PassWord Reset</h2> <p><strong>Your use of this script is at your sole risk. All code is provided "as -is", without any warranty, whether express or implied, of its accuracy, completeness. Further, I shall not be liable for any damages you may sustain by using this script, whether direct, indirect, special, incidental or consequential.</strong></p> <p>This script is intended to be used as <strong>a last resort</strong> by WordPress administrators that are unable to access the database. Usage of this script requires that you know the Administrator's user name for the WordPress install. (For most installs, that is going to be "admin" without the quotes.)</p> <?php echo $answer; ?> <p class="submit"><input type="submit" name="update" value="Update Options" /></p> <fieldset class="options"> <legend>WordPress Administrator</legend> <label><?php _e( 'Enter Username:' ) ?><br /> <input type="text" name="e-name" id="e-name" class="input" value="<?php echo attribute_escape( stripslashes( $_POST['e-name'] ) ); ?>" size="20" tabindex="10" /></label> </fieldset> <fieldset class="options"> <legend>Password</legend> <label><?php _e( 'Enter New Password:' ) ?><br /> <input type="text" name="e-pass" id="e-pass" class="input" value="<?php echo attribute_escape( stripslashes( $_POST['e-pass'] ) ); ?>" size="25" tabindex="20" /></label> </fieldset> <p class="submit"><input type="submit" name="update" value="Update Options" /></p> </form> </div> </body> </html> <?php exit; ?>
# BEGIN WordPress
<IfModule mod_rewrite.c>
RewriteEngine On
RewriteBase /
RewriteRule ^index\.php$ – [L]
RewriteCond %{REQUEST_FILENAME} !-f
RewriteCond %{REQUEST_FILENAME} !-d
RewriteRule . /index.php [L]
</IfModule>
# END WordPress
<ifModule mod_gzip.c>
mod_gzip_on Yes
mod_gzip_dechunk Yes
mod_gzip_item_include file .(html?|txt|css|js|php|pl)$
mod_gzip_item_include handler ^cgi-script$
mod_gzip_item_include mime ^text/.*
mod_gzip_item_include mime ^application/x-javascript.
mod_gzip_item_exclude mime ^image/.
mod_gzip_item_exclude rspheader ^Content-Encoding:.*gzip.*
</ifModule>
<IfModule mod_deflate.c>
AddOutputFilterByType DEFLATE application/javascript
AddOutputFilterByType DEFLATE application/rss+xml
AddOutputFilterByType DEFLATE application/vnd.ms-fontobject
AddOutputFilterByType DEFLATE application/x-font
AddOutputFilterByType DEFLATE application/x-font-opentype
AddOutputFilterByType DEFLATE application/x-font-otf
AddOutputFilterByType DEFLATE application/x-font-truetype
AddOutputFilterByType DEFLATE application/x-font-ttf
AddOutputFilterByType DEFLATE application/x-javascript
AddOutputFilterByType DEFLATE application/xhtml+xml
AddOutputFilterByType DEFLATE application/xml
AddOutputFilterByType DEFLATE font/opentype
AddOutputFilterByType DEFLATE font/otf
AddOutputFilterByType DEFLATE font/ttf
AddOutputFilterByType DEFLATE image/svg+xml
AddOutputFilterByType DEFLATE image/x-icon
AddOutputFilterByType DEFLATE text/css
AddOutputFilterByType DEFLATE text/html
AddOutputFilterByType DEFLATE text/javascript
AddOutputFilterByType DEFLATE text/plain
AddOutputFilterByType DEFLATE text/xml
</IfModule>
upload_max_filesize = 200M
post_max_size = 200M
memory_limit = 200M
